National Vulnerability Database published a notification of a Gutenberg plugin vulnerability.
The United States government’s National Vulnerability Database published a notification of a vulnerability discovered in the official WordPress Gutenberg plugin. But according to the person who found it, WordPress is said to have not acknowledged it’s a vulnerability.
| Software | Gutenberg |
| Type | Plugin |
| Vulnerable versions | 13.7.2 |
| Fixed in | 13.7.3 |
| Classification | Cross Site Scripting (XSS) |
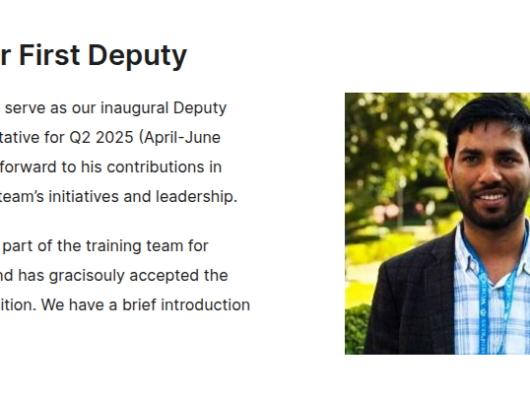
| Credits | Sumit Singh |
Update the WordPress Gutenberg plugin to the latest available version (at least 13.7.3).
Stored Cross-Site Scripting (XSS) Vulnerability
XSS is a type of vulnerability that happens when someone can upload something like a script that wouldn’t ordinarily be allowed through a form or other method.
Most forms and other website inputs will validate that what’s being updated is expected and will filter out dangerous files.
An example is a form for uploading an image that fails to block an attacker from uploading a malicious script.
According to the non-profit Open Web Application Security Project, an organization focused on helping improve software security, this is what can happen with a successful XSS attack:
Common Vulnerabilities & Exposures – CVE
An organization named CVE serves as a way for documenting vulnerabilities and publicizing the discoveries to the public.
The organization, which the U.S. Department of Homeland Security supports, examines discoveries of vulnerabilities and, if accepted, will assign the vulnerability a CVE number that serves as the identification number of that specific vulnerability.
Discovery Of Vulnerability In Gutenberg
Security research discovered what was believed to be a vulnerability. The discovery was submitted to the CVE, and the discovery was approved and assigned a CVE ID number, making the discovery an official vulnerability.
The XSS vulnerability was given the ID number CVE-2022-33994.
That means that someone with Contributor level privileges can cause a malicious file to be inserted into the website.
The way to do it is by inserting the image through a URL.
In Gutenberg, there are three ways to upload an image.
- Upload it
- Choose an existing image from the WordPress Media Libary
- Insert the image from a URL
That last method is where the vulnerability comes from because, according to the security researcher, one can upload an image with any extension file name to WordPress via a URL, which the upload feature does not allow.
Is It Really A Vulnerability?
The researcher reported the vulnerability to WordPress. But according to the person who discovered it, WordPress didn’t acknowledge it as a vulnerability.
So it seems that there is a question as to whether WordPress is right and the U.S. Government-supported CVE foundation is wrong (or vice-versa) about whether this is an XSS vulnerability.
The researcher insists that this is a real vulnerability and offers the CVE acceptance to validate that claim.
Furthermore, the researcher implies or suggests that the situation where the WordPress Gutenberg plugin allows uploading images via a URL might not be a good practice, noting that other companies do not allow that kind of uploading.